We’ve been a little more proactive lately about suggesting that people change their passwords from time to time. Usually, passwords are the annoying step standing between us and our data. We use them so often, and they’re so familiar, that we can become careless about them. Here are five recommendations for better passwords.
Email passwords are really important. In most cases, password resets can be done through email. If you go to Facebook, for example, and tell them you forgot your password, you can reset it if you have access to the email account tied to the Facebook one. The same is true for most online services. If you have access to email, you can get access to almost every account tied to that email address. So your email password should be among your most heavily guarded.
Be careful about tying accounts together. It’s really tempting to use that “Login with Facebook” or “Login with Google Plus” link on that neat web site you want to try out so you don’t have to set up a separate account. But be careful doing that. In some cases, you may be making connections between those accounts that you don’t want. Maybe I don’t need Facebook to know that I’m using this tool. Or maybe I don’t want this new tool to be posting things on my Facebook wall. While the promise of one login for everything is really attractive, make sure you understand how the data moves between the sites, and what you’re giving them permission to do.
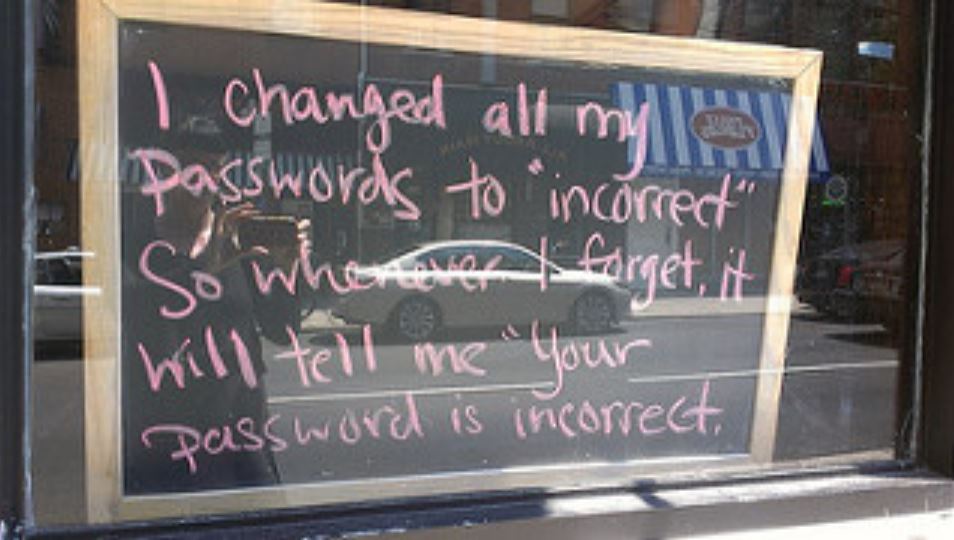
Change your passwords. The old adage is that your password is like your underwear. Don’t leave them lying around. Change them once in a while. Don’t share them with friends. Sometimes, despite our best efforts, passwords get out. Maybe there was malware on a computer you used. Maybe some web site got hacked and was storing passwords in a format that made it possible to steal them. Maybe someone saw you type in a password and figured it out. If you change your password once in a while, you reduce the possibility that someone will be able to exploit one of these kinds of indiscretions. It’s also a good idea to use different passwords on each site, and a password manager to keep track of them all. That way, if one of your passwords does get out, it doesn’t give the attacker access to all of your online accounts.
Complicated passwords are good passwords. If someone can guess your password, they can become you online. Computer programs can be written to guess passwords, and they’re really fast. A “brute force” attack tries every possible password until it hits on the right one. There are products available that can try 3 million passwords per second. You want a long password that’s not easy to guess.
Let’s take a very simple case. Suppose your password is one character long, and that it’s a number. If I’m trying to guess your password, there are only 10 possible passwords for you to have. So it will be very easy for me to guess it. Now, suppose instead that your password can be a letter or a number. Now, there are 36 possible passwords. That’s a little better. But what if we use both lower-case and upper-case letters, as well as numbers and punctuation symbols? A quick look at my keyboard shows 95 possible values. This gets really powerful as the length of the password increases. So a standard 4-character pin that you would use to access your ATM or open your garage door would have 10 x 10 x 10 x 10 = 10000 possible values. But if it could include all 95 characters on the keyboard, it would have 95 x 95 x 95 x 95 = 81450625 possible values. That’s a lot harder to guess. There’s a whole science called information entropy behind all this if you’re interested.
And if you make it a long password, that’s even better. An 8-character password is 95 times as good as a 7-character password. If you want a pretty good password, try using a passphrase instead. If I use “Four score and 7 years ago!” as my password, I have a 27-character password that includes uppercase, lowercase, numbers, and punctuation. While it’s still not a fantastic password because of the dictionary words, it’s a lot better than the name of your cat, or your child’s birthday. Plus, it’s easy to remember.
All passwords suck. Passwords are a holdover from a time when we didn’t have such fantastic computing power. We’re at the point now where just about any password can be cracked if given enough time and resources. And because passwords must be remembered and entered frequently, we tend to use some of the easier-to-guess ones. If I use “MfABKSsnaQVDcdgIIpityTxX2yn” as my 27-character password instead of the opening of the Gettysburg Address, it’s much less likely to be guessed. But I’m also much less likely to remember it.
Ultimately, we’re going to reach the point where computing power is so advanced that any password that provides even a modest amount of security will be too cumbersome and impractical to actually use. To solve that problem, we’ll need multi-factored authentication. You really have that now. Think back to the ATM example I mentioned earlier. What’s to keep someone from walking up to an ATM machine and guessing your password? After all, there are only 10,000 combinations of four digits. It’s not very secure at all. The reason ATM cards don’t get hacked all the time is that you have to actually have the card to use the password. The authentication has two factors: something you have (the card) and something you know (the pin). To get access to the account, you have to have both.
On my Google account, I have two-factor authentication turned on. If someone tries to log in to my Gmail account, it sends a text message to my phone with a six-digit code. I have to type that code in to the web browser to log in. That way, I have to know my password, but I also have to prove that I have access to my cell phone. It’s a little less convenient, but it’s a lot more secure.
Proving who you are online is difficult, and it’s getting harder. But being diligent about password management can help you avoid identity theft problems.
Photo credit: Lulu Hoeller on Flickr.
